 The security triad (also known as the CIA triad) defines the overarching principles of information security. One of the triad’s primary principles is assuring the integrity of data. The goal of this principle is to provide assurance that the data has not been modified, tampered with, or corrupted in any way, and the method most often used to do this is called hashing.
The security triad (also known as the CIA triad) defines the overarching principles of information security. One of the triad’s primary principles is assuring the integrity of data. The goal of this principle is to provide assurance that the data has not been modified, tampered with, or corrupted in any way, and the method most often used to do this is called hashing.
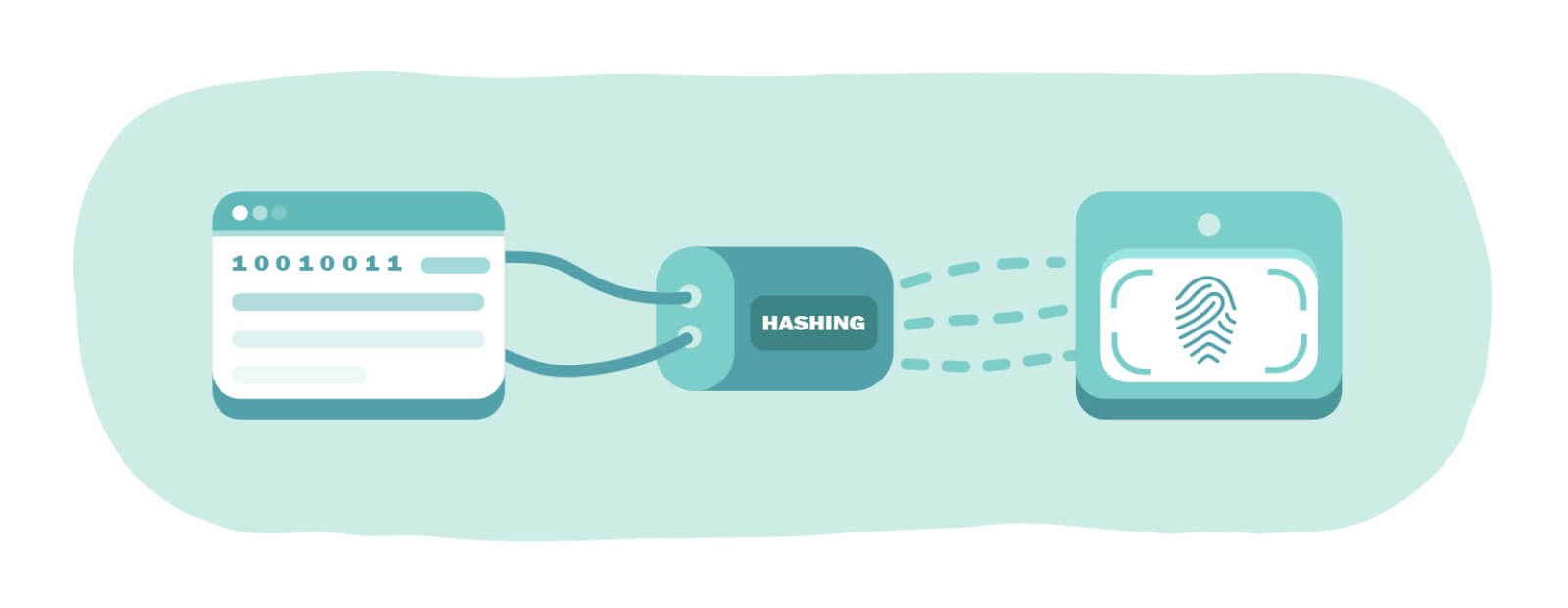
What is Hashing?
There are three key components involved in the hashing process: input, hash function, and hash value. The input is the data itself, which can be any size and take any form such as a text file, Microsoft PowerPoint presentation, MP3 music file, etc. The hash function is the algorithm used to generate the fingerprint. The hash value is the output of that hash function, which is the resultant fingerprint of the input data.
It’s important to note, however, that the hash value is a fixed size regardless of the input data size. The size of the output depends on the algorithm used. To illustrate this, let’s look at an example.
The MD5 hash value for the opening paragraph of this document is:
fb84fe5514eebe360ec434bc326c70d2
The MD5 hash for Ernest Hemingway’s novel The Old Man and the Sea is:
e6200a8a14a76ce2e19bac3f48d2f036
Properties of Hash algorithm
In order to be considered viable, there are four goals that a hash algorithm needs to meet:
- Running the same hash function on the same input data must yield the same hash value.
- Small changes to input data should result in large changes to the hash value.
- Each resultant hash value for different input data should be unique.
- The hashing process must be one way (i.e. it can’t be reversed).
Common Hash Algorithms
There are many different hash algorithms available for use today. Here are a few of the most common hash algorithms:
- MD5 – One of the most common algorithms, which provides a 128-bit hash value.
- SHA-1 – Provides a 160-bit hash value. Designed by the National Security Agency (NSA).
- SHA-2 – Actually a family of hash algorithms, SHA-2 has several variants that produce different size hash values.
- SHA-3 – Provides variants that produce hash values of the same length as SHA-2, but it corrects some of SHA-2’s weaknesses.
- HMAC – HMAC can use any cryptographic hash function as its base but also appends a secret key to the input data, serving as both a hash function and a message authentication method.
Hashing and Data integrity
Now that we’ve got all the background information, we can see the different ways hashing is used. One use is in verifying data integrity – which is one of the key concepts for information security. In addition, it can also be used to authenticate a sender, not only ensuring that the data remains intact but also making sure of its sender.
Conclusion
As we can see, hashing plays an important role in information security. When considering hashing, there are three important concepts to remember:
- Hashing plays a key role in assuring data integrity.
- Even minor changes to the input data must result in major changes to the hash value output.
- The hashing process must be one way.
Download the White Paper

 Español
Español