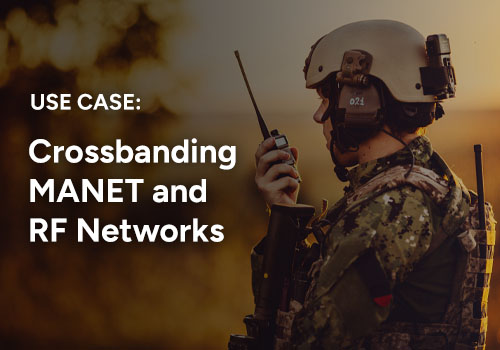
Secure Communications
A multi-layer approach to mission security
In today’s information-intense domain, security is absolutely critical to the success of the mission. But what exactly does the term “security” mean? Often when users talk about security, they use it as a synonym for technology such as encryption, authentication, and validation. REDCOM has a much broader interpretation of security because we focus on the overall security of the mission and think about concepts such as interoperability, resiliency, and ease of use.
Missions can be compromised by a variety of factors, including single points of failure, slow boot times, interoperability challenges, and overly complex technology. Each of these is clearly a security concern, even though they have nothing to do with encryption or validation. This is why REDCOM takes a holistic, multi-layer approach to security.
Home / Secure Communications

Encrypted, tested, validated.
At REDCOM we believe security cannot be achieved through a “bolted on” approach. This is why we build security into all of our products from the start. A strong code base designed with security in mind forms the foundation for all of our military-grade solutions.
REDCOM solutions are:
- Standards-based. REDCOM builds our products to industry standards, which ensures interoperability with a variety of transmission paths, gateways, and endpoints. Users are never locked into proprietary end instruments.
- Encrypted. We invest in the latest forms of encryption, including Suite B, TLS/SRTP, and IPsec. We also allocate significant R&D efforts towards the development of next-generation encryption and authentication technologies.
- Compliant. REDCOM maintains compliance with numerous DISA and NIAP requirements.
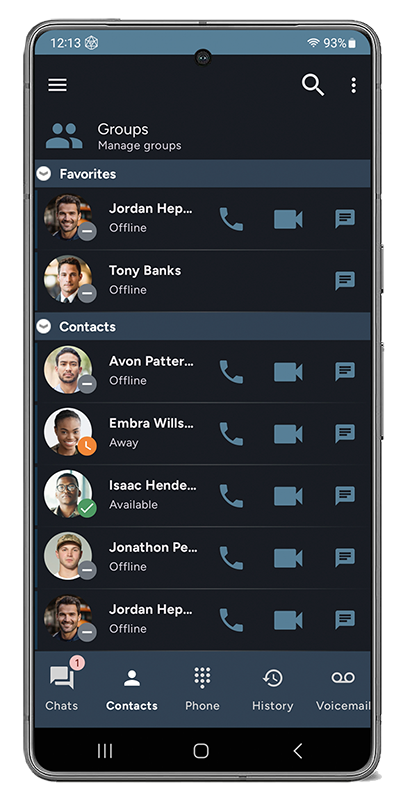
- Validated. REDCOM products such as REDCOM Sigma® and the REDCOM Secure Client for Android have passed FIPS 140-2 validation testing, meaning that we can provide standardized, secure solutions for government agencies by appropriately handling SBU data.
Hardware and software built for resiliency
REDCOM’s integrated approach to product design delivers mission-critical command and control functionality that offsets cybersecurity concerns while enhancing network resiliency. REDCOM solutions are:
- Built for survivability in the field. If the IP-based network is compromised, REDCOM technology allows the sustainment of command and control functions by merely falling back to legacy networks. This level of redundancy allows for the continuity of operations in the limited, intermittent, or denied communication environments.
- Resilient to hard shut-downs. REDCOM systems do not require the operator to “save” the work before shutting down, which makes our systems resilient to hard or unexpected power-off.
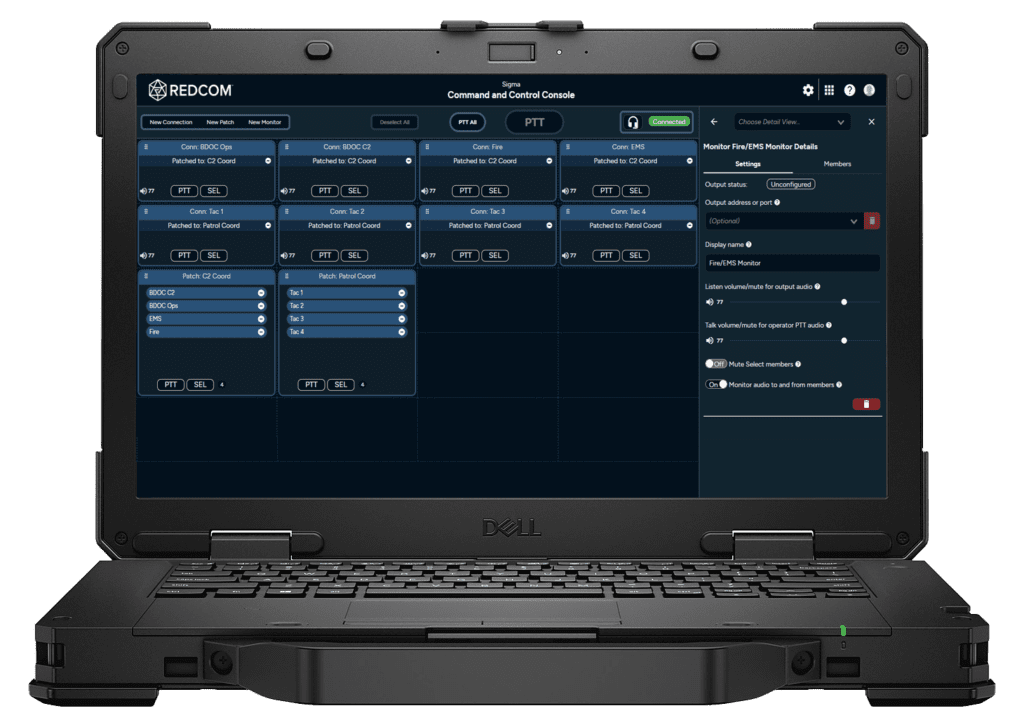
- Quick to boot up. REDCOM platforms feature extremely rapid boot times. These factors make REDCOM technology ideally suited for tactical deployments and are directly aligned with the DoD’s strategy to become more agile.
- Hardened. REDCOM solutions can employ “hardened” components that meet the rigors of harsh tactical environments.
REDCOM Sigma and Auto-PACE
While Auto-PACE is mostly a function of hardware and software at the network level, it’s important to note that as an application, REDCOM Sigma works out of the box with an Auto-PACE network. Sigma also has additional capabilities to automate your communications PACE plan with automated voice routing and redundancy features.
- Alternate Trunk Routing: This Sigma feature leverages separate network paths to connect different nodes on the network. If the primary path cannot establish a connection, Sigma will automatically attempt to connect with an alternate path and will continue this process until either connection is established or all defined paths have been exhausted. These alternate connection paths can be via any IP-based network type, including Wi-Fi, LTE, SATCOM, or MANET.
- Automated routing: Sigma supports traditional telecommunication features known as Hunt Groups and Find Me/Follow Me. These features allow you to configure multiple paths (i.e., primary, alternate, contingency, emergency) to establish a connection with a specific user agnostic to the comms platform. If the primary path cannot establish a connection, the system will automatically attempt to connect through an alternate path. It will continue this process until a connection is established or until it has exhausted all defined paths.
- Redundancy: Sigma redundancy can be achieved with a secondary standby server or by using fault tolerance provided by a hypervisor. A secondary server may require a manual switchover in the event of a failure, while a hypervisor with fault tolerance delivers automatic failover.
Intuitive and easy to use
At REDCOM, we understand that the less users have to think about technology, the more time they have to accomplish their mission. When a national emergency occurs, users do not have the luxury of time to contact tech support or wait for field service reps to resolve issues.
The key to a superior user interface is ‘Human-Centered Design’ which puts the user and their specific needs at the center of every interface. Using this design philosophy, every choice we make as we develop our software requires us to investigate and open up the lines of communication between our team of designers, engineers, and testers. REDCOM actually conducts one-on-one interviews with our end users to seek their input about ways to improve our interfaces and make their lives easier.
REDCOM solutions are:
- Extremely easy to learn. Specialized certifications are not required to get up and running with REDCOM products. Users can learn to configure and operate our hardware and software with very little training.
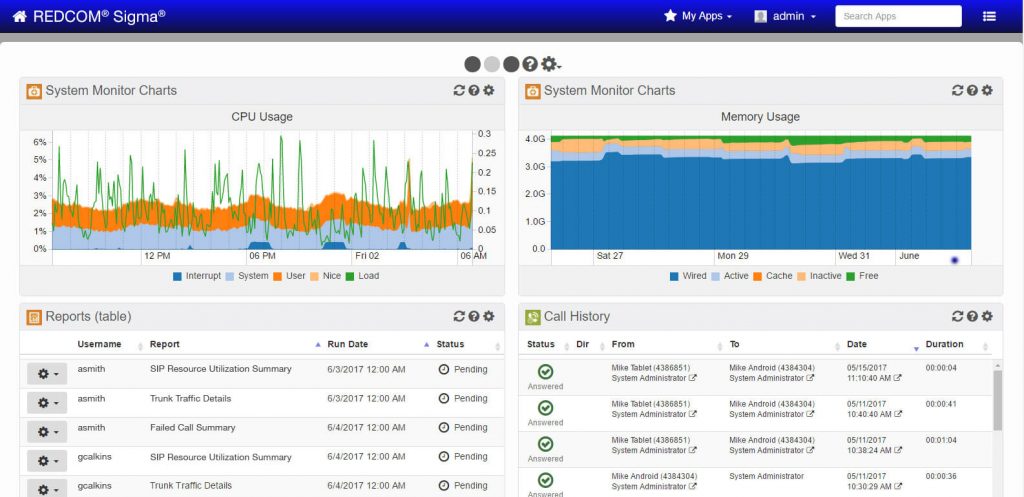
- Designed for serious government use. Our software’s web-based interface was designed specifically with government users in mind. It is easy to navigate, highly customizable, and quick to set up.
- Built around one unified platform. REDCOM software provides one intuitive interface for managing all your comms. Because REDCOM built Sigma on open standards, it supports the technology fielded today while enabling the rapid integration of new solutions as they become available.
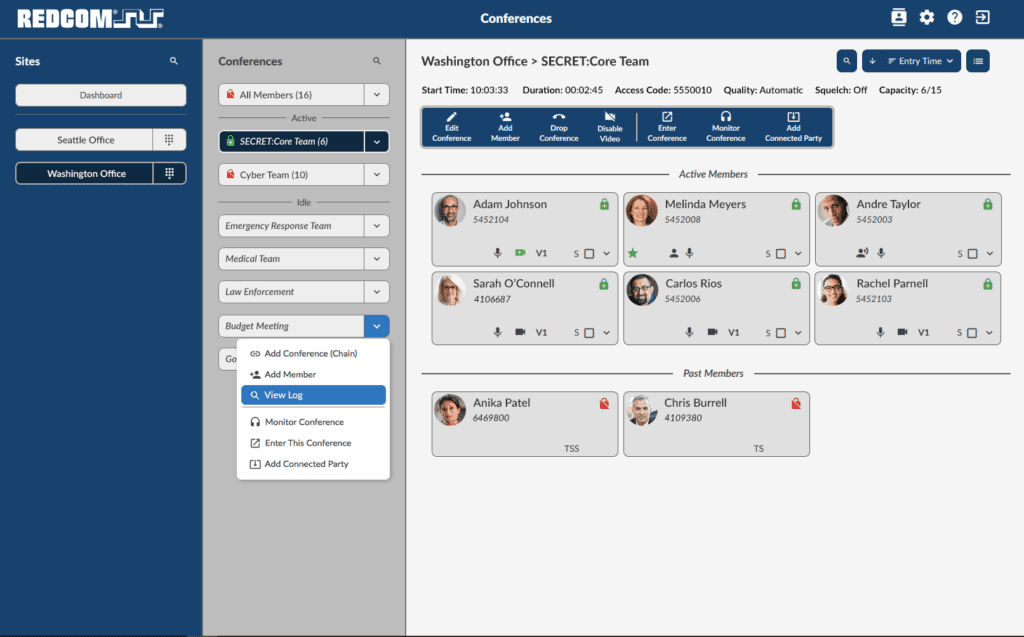
Secure Voice Gateway
REDCOM’s Secure Voice Gateway is an ACC-compliant solution for Type 1 secure voice gateways and conferencing systems. REDCOM Secure Voice Gateway addresses challenges for agencies that require access to red/black networks using a Type 1 gateway device or a Type 1 conferencing solution. REDCOM Secure Voice Gateway is powered by our flagship Sigma C2 software which is JITC-tested and certified.
Key Benefits:
- Easy-to-use secure voice conferencing system
- Enables multi-party ACC-compliant Type 1 communications
- Black side of the network can be anywhere in the world, as long as the endpoints are Type 1 capable devices
- Crystal clear voice quality, on both the red and black side of the network
REDCOM and JITC
What is JITC?
Joint Interoperability Test Command (JITC) a subdivision of the United States Department of Defense that tests and certifies technologies for government and military use. JITC tests technologies that pertain to the multiple branches of the armed services and government. JITC testing ensures only proven capabilities are placed in the hands of our Nation’s warfighters. Once a product is JITC tested and certified it gets on the DoDIN approved product list.
DoDIN Approved Product List
The Department of Defense Information Network (DoDIN) Approved Products List (APL) is the single consolidated list of products that affect communication and collaboration across the DoDIN. The DoDIN APL is an acquisition decision support tool for DoD organizations interested in procuring equipment to add to the DISN to support their mission. The DoDIN APL is maintained by The Defense Information Systems Agency (DISA).
REDCOM JITC tested products
REDCOM Sigma has been tested and certified by JITC and is on the DoDIN approved product list. REDCOM Sigma is approved as a Local Session Controller (LSC). REDCOM Sigma C2 software is our flagship military-grade software Command and Control (C2) platform that delivers robust call control, media handling, and encrypted communications. Sigma is based on open SIP standards, which eliminates proprietary endpoints and applications.
Sigma can function as a stand-alone Local Session Controller (LSC) or as an adjunct to an existing Enterprise Session Controller (ESC) to deliver advanced voice services such as transcoding and conferencing for red and black networks.
- PRODUCT BRIEFS
- USE CASES