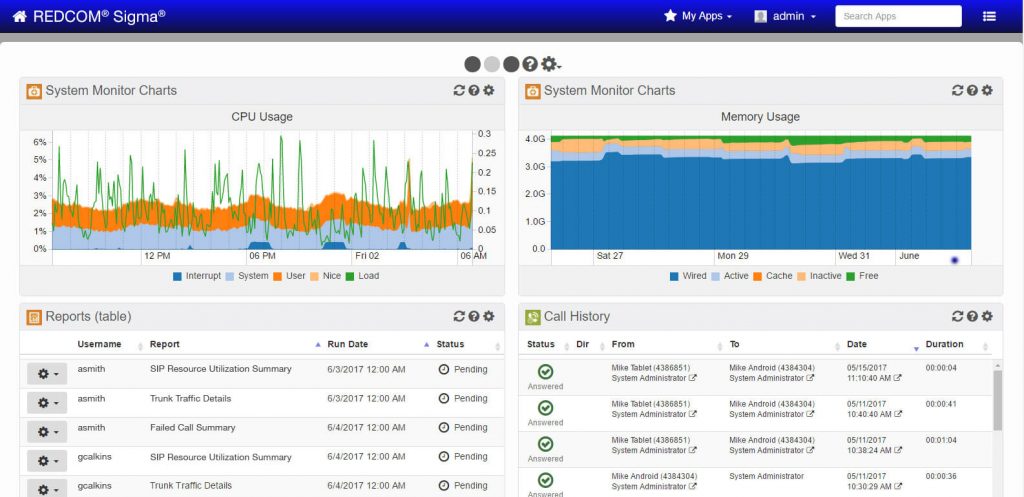
Sigma C2 Software
Core C2 platform with voice, video, & chat
Sigma
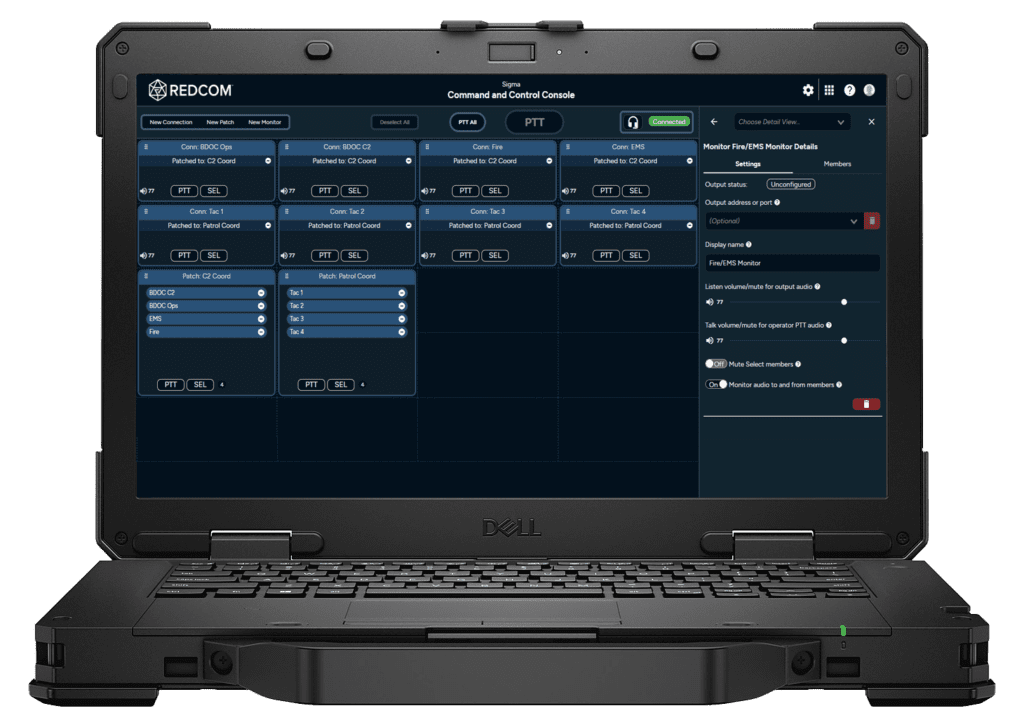
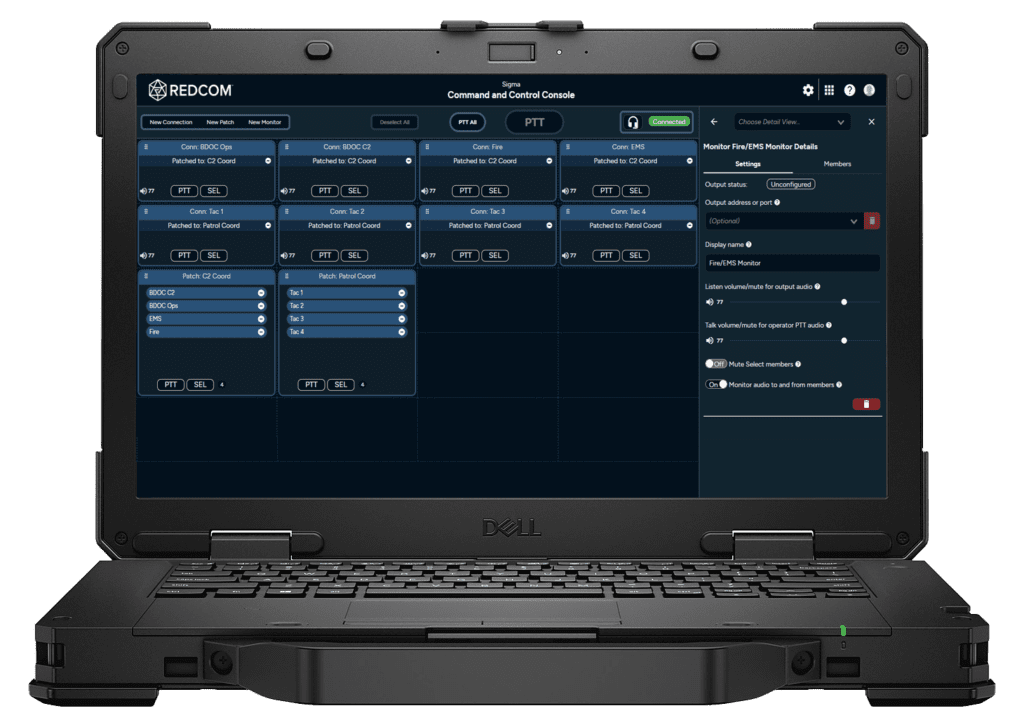
C2 Console
C2 Console
Monitor & Control Tactical Comms
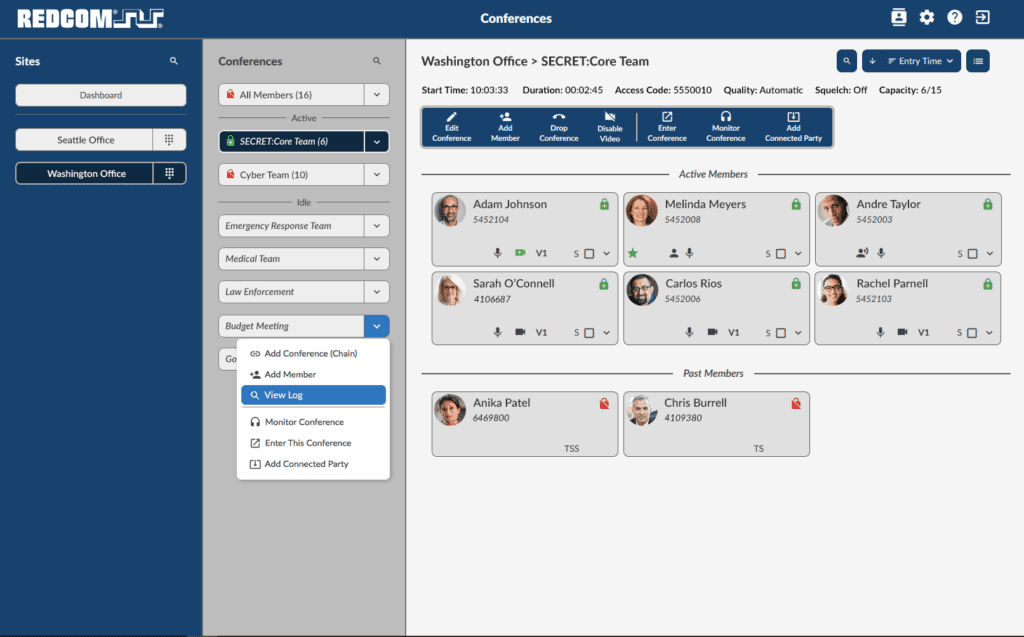
Sigma Conferencing
Manage multi-party voice calls
Sigma
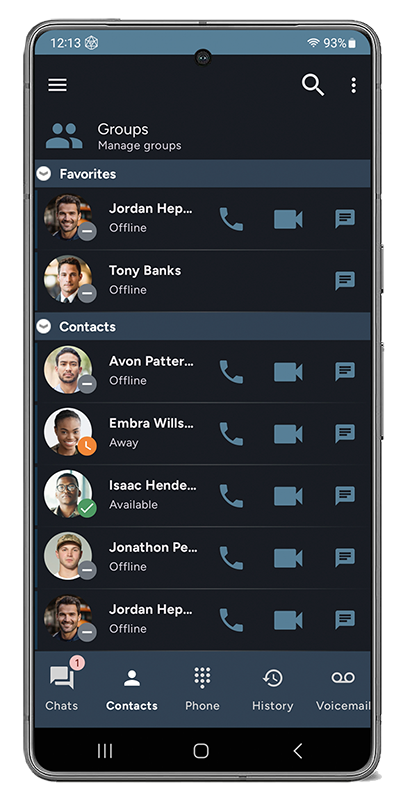
Client
Client
Voice & PTT app for desktop, mobile & ATAK

Sigma
XRI Family
XRI Family
C2 Platform with Radio Interop

Sigma
SVG-1200
SVG-1200
Type 1 Secure Voice Gateway
- Careers
- Partnerships
Capabilites
Products
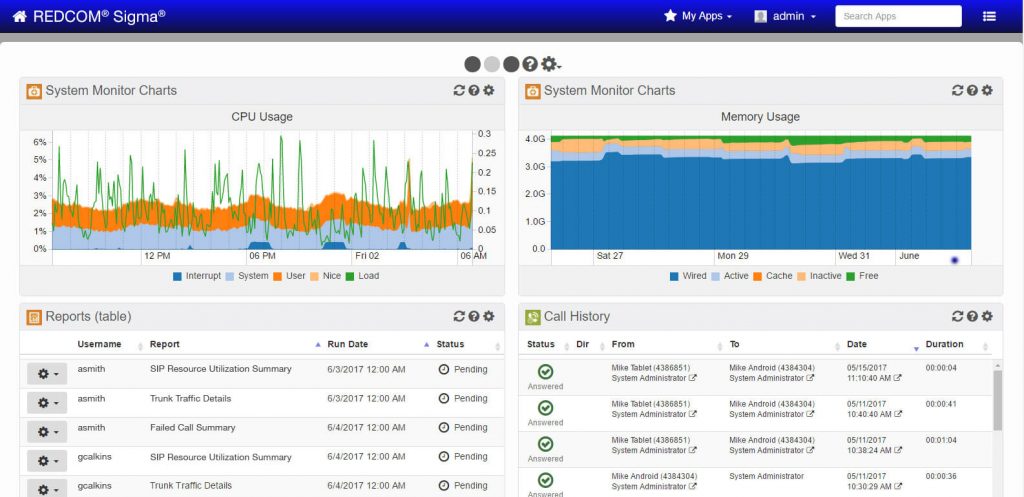
Sigma C2 Software
Core C2 platform with voice, video, & chat
Sigma
C2 Console
C2 Console
Monitor & Control Tactical Comms
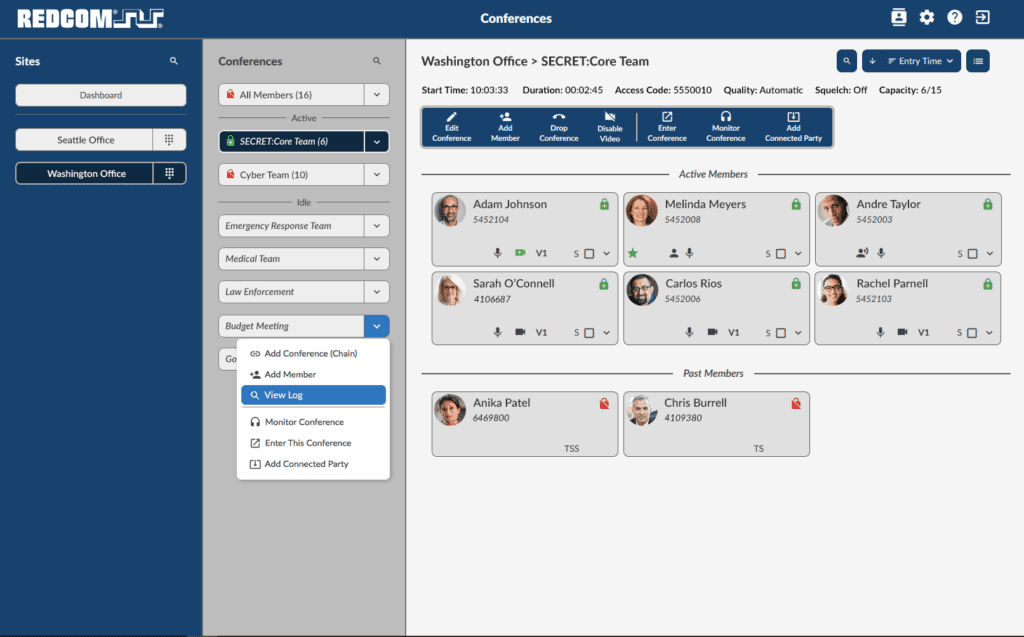
Sigma Conferencing
Manage multi-party voice calls
Sigma
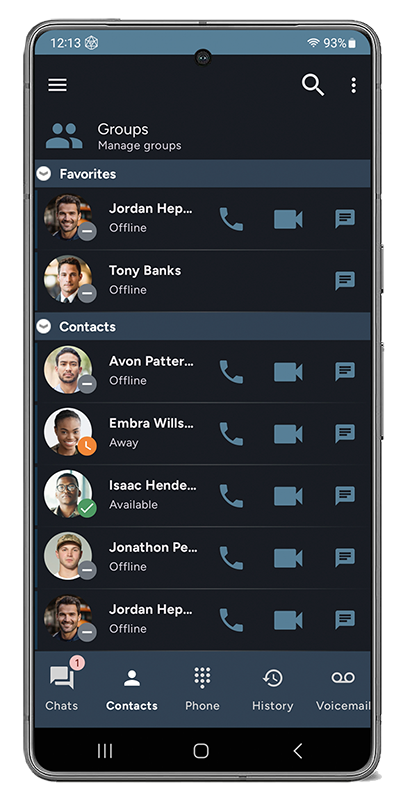
Client
Client
Voice & PTT app for desktop, mobile & ATAK

Sigma
XRI Family
XRI Family
C2 Platform with Radio Interop

Sigma
SVG-1200
SVG-1200
Type 1 Secure Voice Gateway
Resources
Company
- Careers
- Partnerships
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Ut elit tellus, luctus nec ullamcorper mattis, pulvinar dapibus leo.