The DoD’s Next Operational Cloud | REDCOM & Klas Webinar

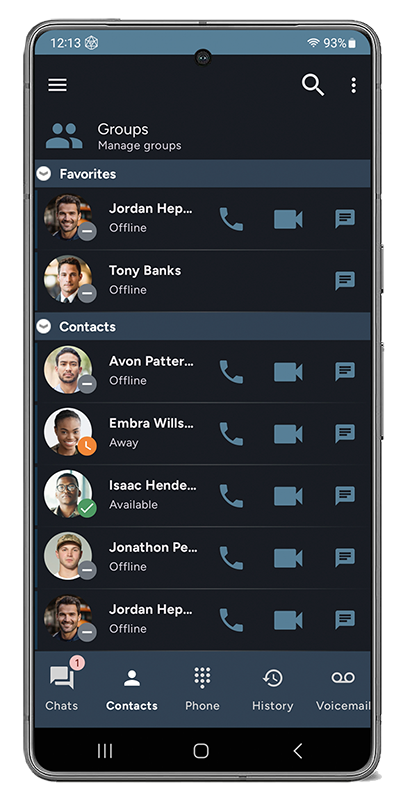
In this webinar, we learned about this powerful joint solution from REDCOM and Klas Government that promises to expand voice, video, and chat communications, improve interoperability, and foster data-driven decision-making.
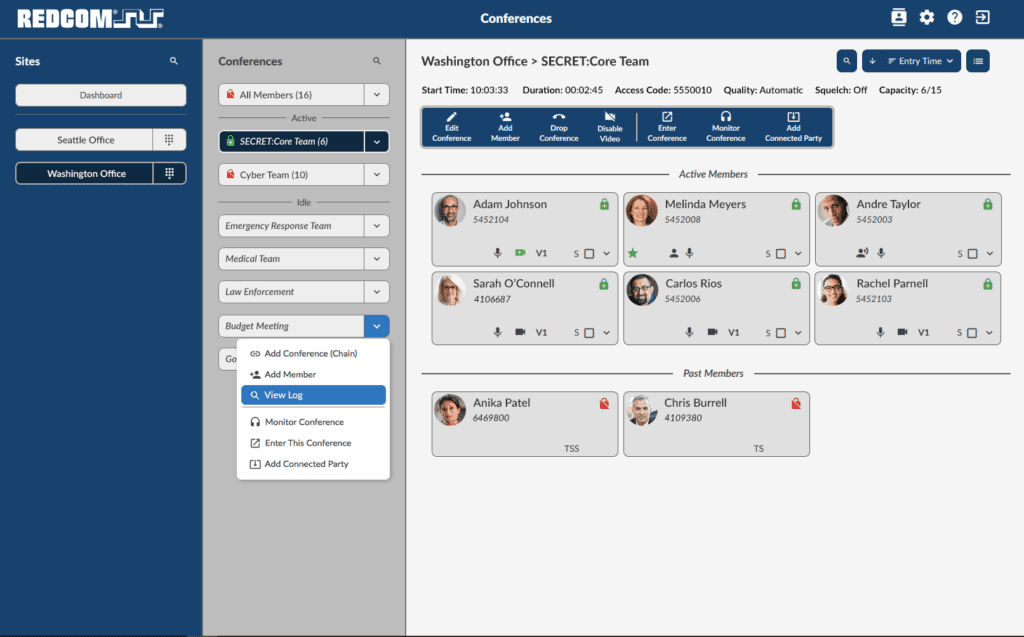
NSA-Certified & ACC-Compliant Solution for Type 1 Secure Conferencing

When matters of national security are on the line, mass-market communications solutions simply won’t cut it. Two of the biggest names in communications — REDCOM and General Dynamics Mission Systems — have partnered to bring to market the only NSA-Certified and ACC-Compliant Solution for Type 1 Secure Voice Conferencing. Watch the Webinar.
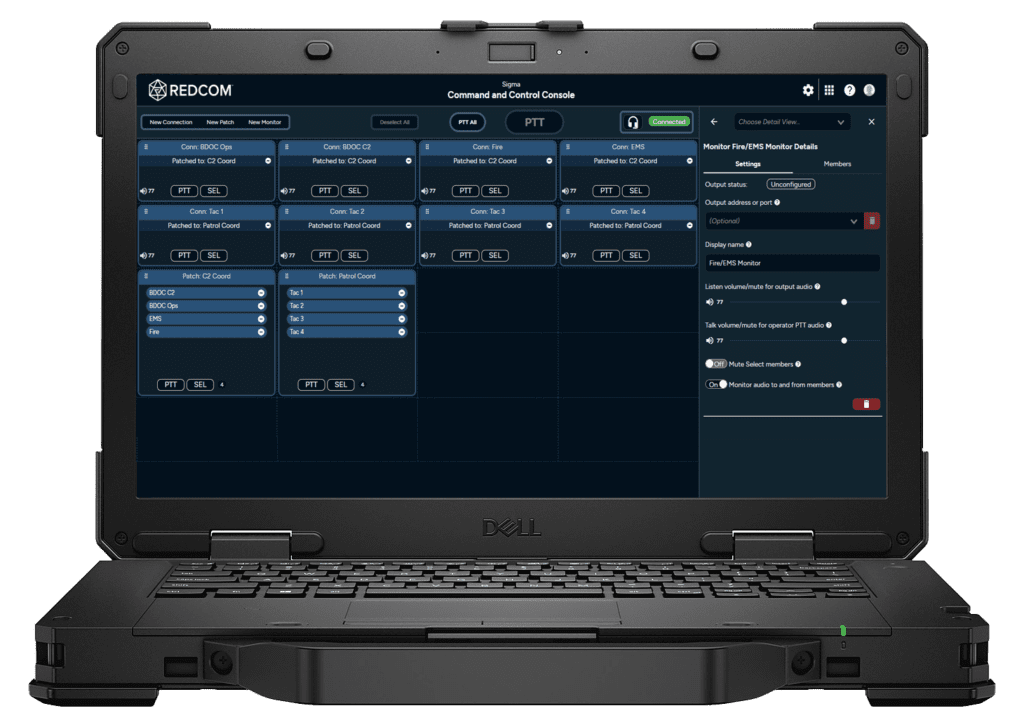
C2 Communications for Next-Gen Superiority

In this webinar, we’ll explore a few of the major new features REDCOM has introduced on the Sigma platform in spring 2022. The first of these is TSM talk group support, which allows Sigma to integrate seamlessly with TSM mesh networks. The second major feature is an integrated C2 console, which gives warfighters a single pane of glass for monitoring and controlling all communications on the tactical network.
Webinar: Zero Trust Architectures for the Tactical Edge

Zero Trust Architecture (ZTA) is an exciting theoretical approach to total information security, but it is just that – an approach. While ZTA technologies are already being developed, tested, and implemented, it is important to not lose sight of the ripples which changes in the enterprise will cause downstream to the edge.
Building to Future Requirements Today | Future Soldier 2021

REDCOM’s Courtney Stiles and Sal Ceravolo present on building to future requirements today at the 2021 virtual Future Soldier Technology Conference.
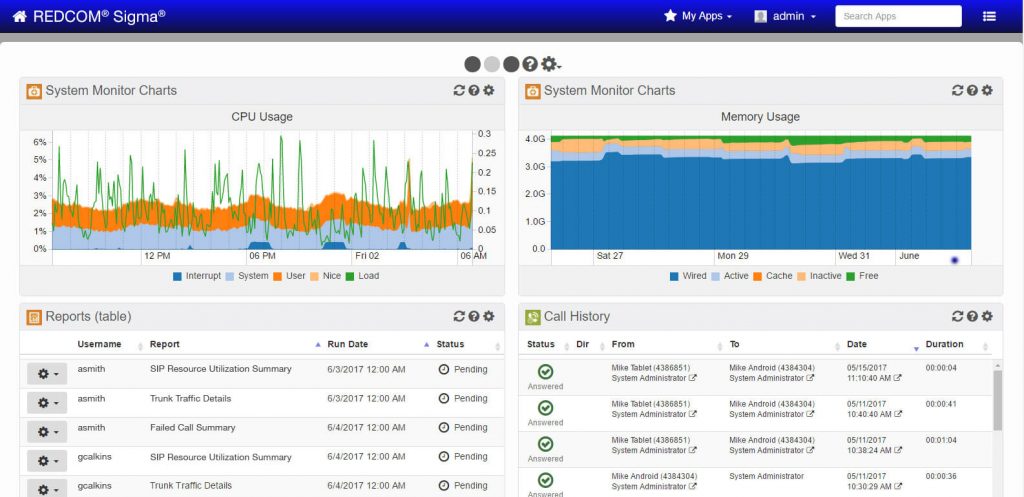
Government-Grade Secure Communications & Conferencing

REDCOM leads a discussion on two REDCOM solutions that are proven in multiple government agencies and enterprise settings, REDCOM Secure Voice Gateway, and REDCOM Conference Manager.
Enhancing Unity of Effort for C2 at the Tactical Edge

In the webinar hosted by AFCEA, REDCOM’s Courtney Stiles and John Kelliher discuss how the new Sigma XRI delivers enhanced Joint/Coalition interoperability, mobility, flexibility, and ease-of-use to the tactical environment, enhancing comms across all echelons.
Command and Control for the Tactical Edge

The United States Army is currently undergoing a massive network modernization effort spanning multiple programs. REDCOM’s C2 communication solutions are a critical part of these programs at the battalion down to the squad.
Securing the Mission

What exactly does the term “security” mean? While encryption is important and very much central to security, we believe mission security hinges on three other factors working together with encryption and validation: interoperability, ease of use, and resiliency.
Cleared for Conferencing

When connecting multiple co-workers and customers, conference calls are usually the platform for collective communications. If your conversations are sensitive or proprietary, protecting the call is of utmost importance.