The Need for Secure Conferencing
The Need for Secure Conferencing
The global pandemic has forced workers and executives across industries to transition to remote work. Companies and government agencies alike have turned to widely available commercial conferencing tools to maintain a semblance of collaboration and information sharing. These mass-market conferencing solutions are sufficient in many scenarios, but fall short in three key areas: security, capacity, and control.
Security. For sensitive communications that demand a secure connection, can you trust software that hosts your meeting on an unknown server? C-Suite execs discussing their company’s strategic direction and government agencies addressing issues of national security clearly need a most robust solution.
Capacity. Mass-market conferencing tools often top out at 100 participants, but let’s be honest, managing a conference with more than a few dozen attendees quickly becomes an exercise in frustration. In these scenarios, participants often find themselves talking over one another and getting interrupted by random background noise.
Control. Commercially available conferencing solutions offer no specialized operator controls, which is critical in large conferences or those during a crisis response scenario. Perhaps several participants need to have an off-topic sidebar discussion. Maybe a single participant needs urgent attention but is unable to break into the larger discussion. There could be two different teams holding separate conferences discussing the same situation without any easy mechanism to join the two. These types of problems are difficult to manage using traditional voice conferencing tools.
Complete Conferencing Solution
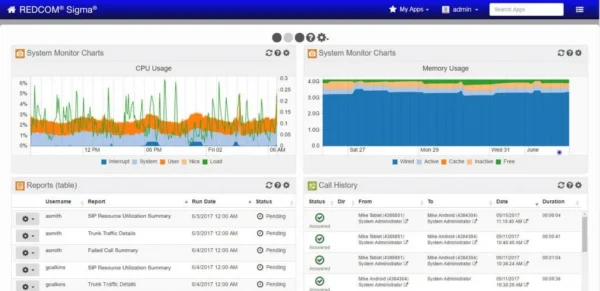
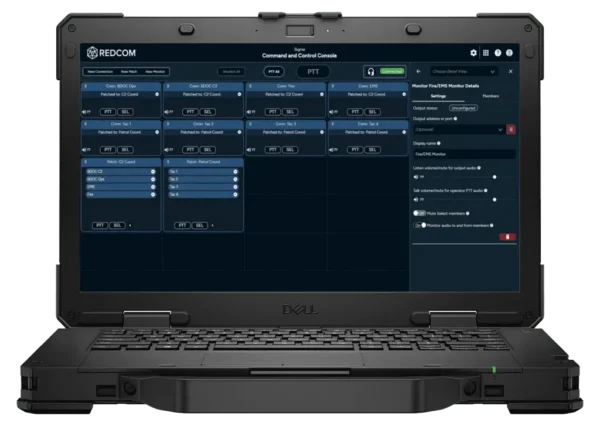
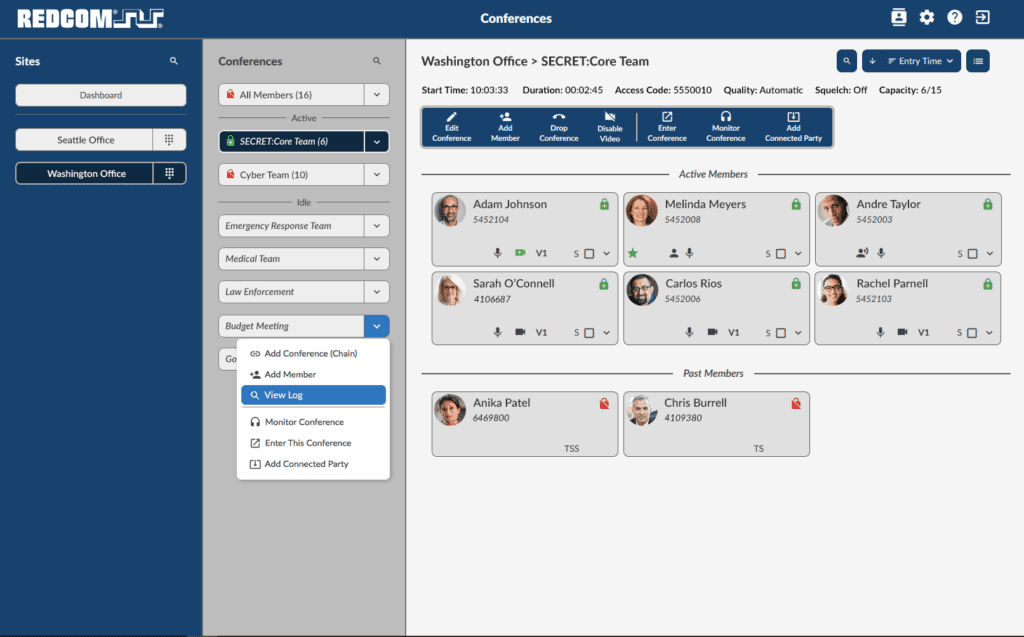
The REDCOM Conference Manager provides a powerful set of tools for monitoring and managing many different conferences — large and small — across several different sites simultaneously. REDCOM’s Conference Manager offers a variety of capabilities to manage and control not only the conferences as a whole, but individual attendees as well. Additionally, the REDCOM Conference Manager is endpoint-agnostic and will work with any device including smartphones, desk phones, softphones, and even radios.
Secure Conferencing Controls. The Conference Manager was built with secure communications in mind and supports multiple levels of access security, flexible conferee screening, and voice encryption to protect confidential discussions and avoid corporate espionage. Additional security features include secure voice between any endpoint via TLS/SRTP, robust access control by user ID, ANI, PIN code or clearance level, security level knockdown, and more.
Full Conference Control. The REDCOM Conference Manager gives admins robust control over all aspects of multiple conferences in real-time. Conference managers can quickly access contacts through a built-in phone book, initiate a conference, and add/drop attendees with the click of a button. Additionally, managers can combine separate conferences into a single larger conference, split a single conference into multiple smaller conferences, create a sidebar conference for select attendees, as well as move attendees between conferences.
Attendee visibility. With the REDCOM Conference Manager, operators have detailed visibility of all conference participants. They can instantly see a user’s security clearance level, talking status, and even tell if that user’s talk path is secure.
The REDCOM Conference Manager is the perfect solution for government agencies, military organizations, and enterprises that need to be able to bring multiple attendees together quickly, securely, and reliably. Indeed, REDCOM’s solution is already in use at multiple government agencies and has reduced the complexity and enhanced flexibility and responsiveness for its users.