REDCOM takes a holistic, multi-layer approach to security that goes beyond typical measures such as encryption and validation. Take a look at our Secured Communications paper that discusses REDCOM’s stance on overall mission security, which necessitates a strong focus on encryption, resiliency, interoperability, and ease of use. Take a look at the previous parts of the Securing the Mission Series: Technology, Resiliency, and Interoperability.
Ease of Use 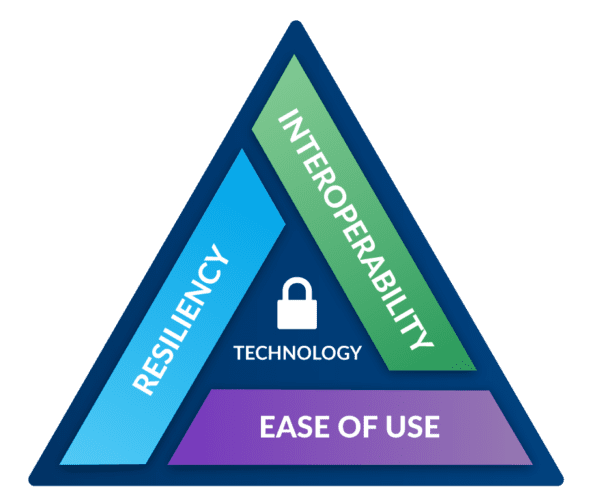
At REDCOM, we understand that the less users have to think about technology, the more time they have to accomplish their mission. Warfighters do not have the luxury of time to contact tech support or wait for field service reps to solve IT issues.
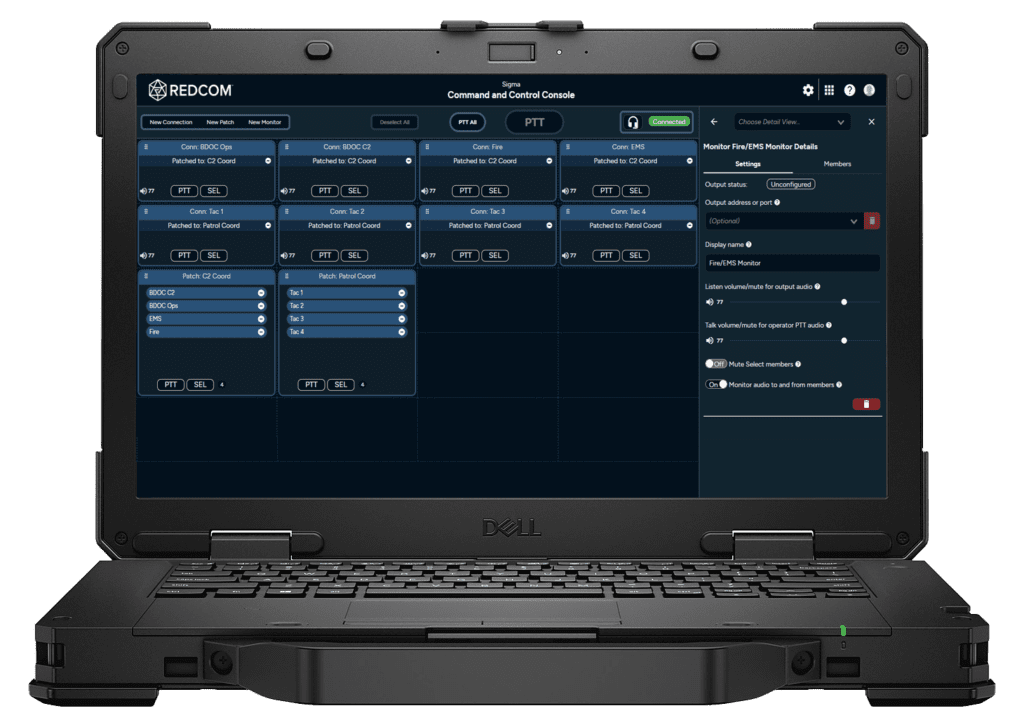
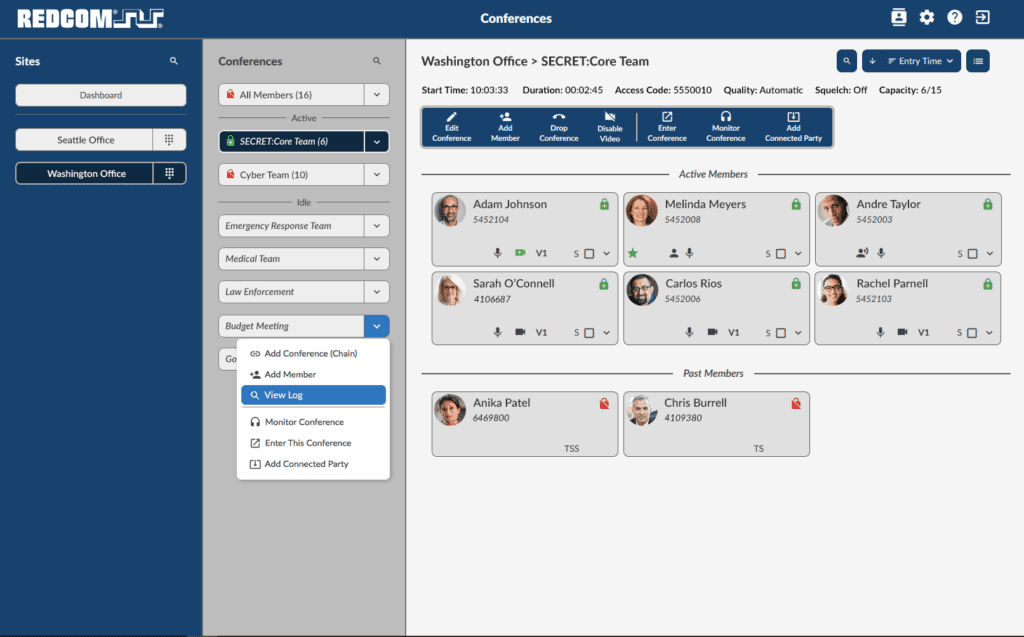
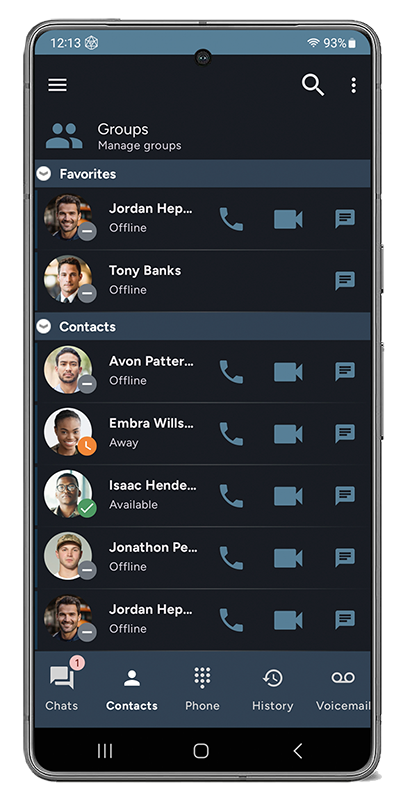
REDCOM recognizes the importance of a simple and intuitive user interface that enables the warfighter to “shoot, move, communicate.” The key to a superior user interface is ‘Human-Centered Design’ which puts the user and their specific needs at the center of every interface.
Using this design philosophy, every choice we make as we develop our software requires us to investigate and open up the lines of communication between our team of designers, engineers, and testers. REDCOM actually conducts one-on-one interviews with our end users to seek their input about ways to improve our interfaces and make their lives easier.
REDCOM solutions are:
- Extremely easy to learn. Specialized certifications are not required to get up and running with REDCOM products. Users can learn to configure and operate our hardware and software with very little training.
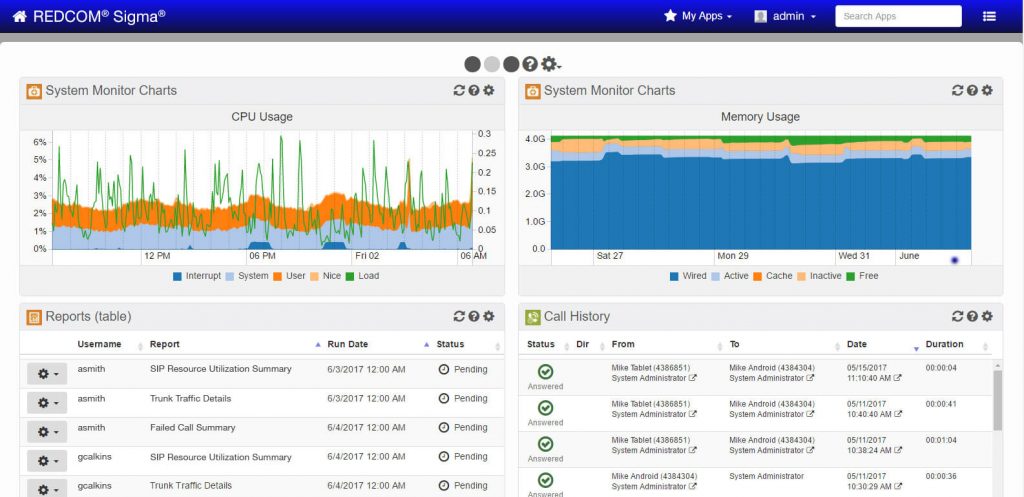
- Built for the warfighter. Our software’s web-based interface is easy to navigate, highly customizable, and quick to set up. This eliminates the armed forces’ requirement for industry field service representatives.
Want to know more about REDCOM’s stance on securing the mission at the tactical edge? Check out a recent webinar, hosted by REDCOM Government Account Manager, Courtney Stiles.