Many systems claim to be secure, provide secure functionality, and may even be validated by an accredited security industry. However, what does it mean to be a good — or even usable — voice-based security system? What makes a secure voice platform exceptional?
We’ve identified four characteristics that we believe are common among secure communication systems that surpass the competition: governance, resiliency, user experience, and interoperability.
Governance
If a company states that security is a primary tenant of its business model, then security must be embedded into the very fabric of the organization’s operations. Often, a company’s board of directors allocates very little time discussing the topic of voice security, and the expertise isn’t present enough to address this area of risk. Security should start at the C-Suite level, and this executive involvement sets the tone for cybersecurity in an organization.
Resiliency
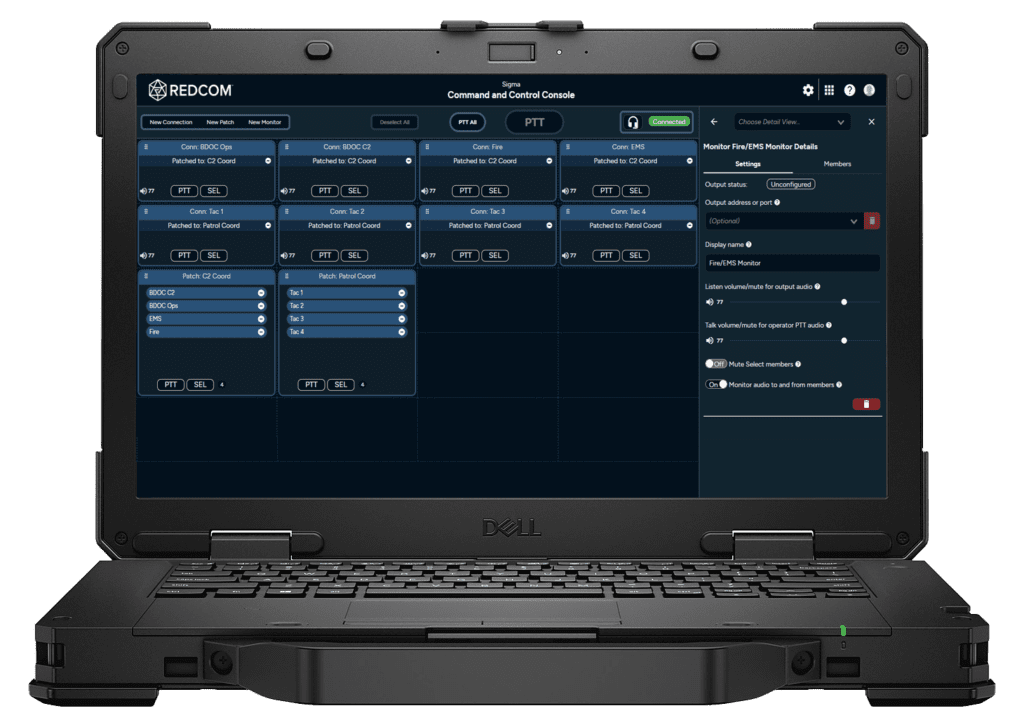
In 2017, Army Chief of Staff Gen. Mark Milley stated that “the network we have today isn’t the network we need for that fight”. Resiliency is an important topic today due to our dependence on cyber systems, and Warfighters need to know that their applications will work without fail on the battlefield – not just in the lab. When striving for resiliency, one must look at five key characteristics that make up a resilient system: attack surface, integrity, availability, survivability, and confidence.
User Experience
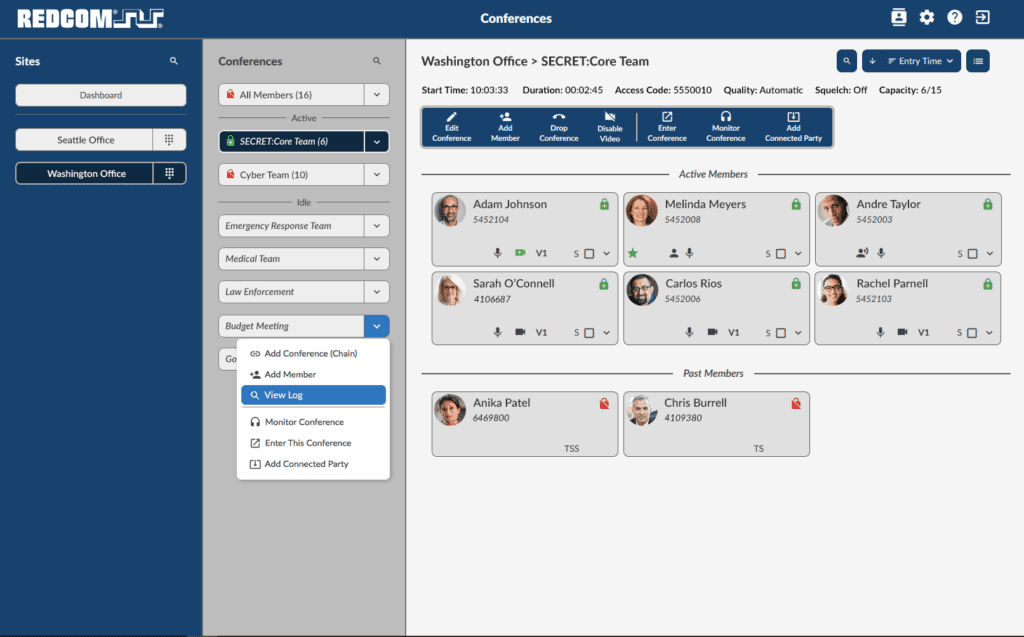
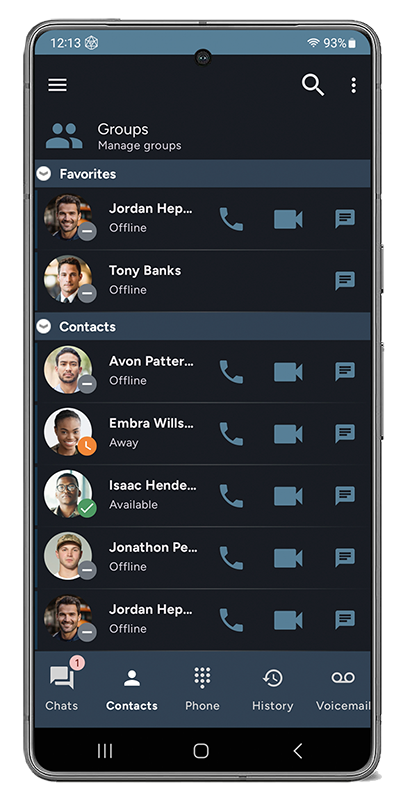
User experience (UX) is a person’s perceptions and responses that result from the use and/or anticipated use of a product, system, or service. It is assumed that computer security and computer usability are inversely proportional to one another, but that is not the case. A system which is secure is more reliable, more controllable, and hence, more secure. At the end of the day, great UX reduces confusion regarding cybersecurity and is thus more likely to encourage a secure environment.
Interoperability
Companies that provide secure voice communication solutions should be validated against a common set of standards and against other validated solutions to guarantee a level of interoperability and security. One of the best interoperability and cybersecurity validations is DISA’s Joint Interoperability Test Command, where a product goes through two phases of certification. JITC supports the Warfighter in their efforts to manage information on and off the battlefield.
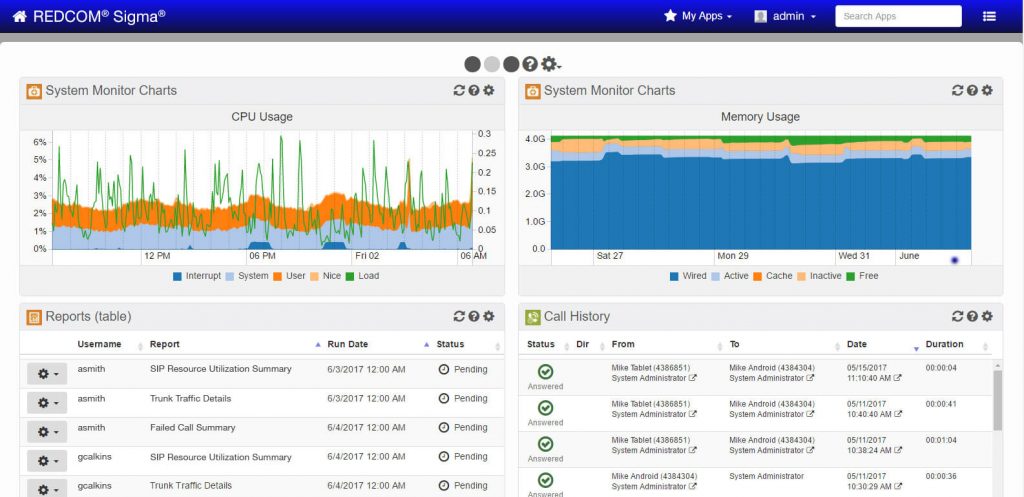
REDCOM’s Take
REDCOM prioritizes security, as a fundamental element of our business model. From C-Suite to engineering, security is embedded into the very fabric of our operations. REDCOM remains at the forefront of the secure voice market, making us the call controller of choice for the tactical edge.
Want to learn more? Download our White Paper on Voice Security ++ for more in-depth insight.